CyberSecurity Part 2: OPSEC and Post-it Note Passwords
By Tony DePrato | Follow Me on LinkedIn
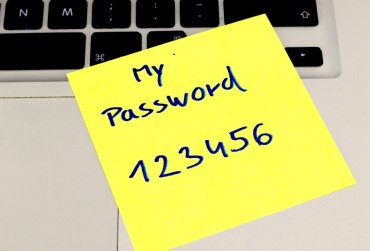
How many times have you seen it? You walk into an office or classroom, and a Post-it is proudly announcing a user’s password. Why? Because schools are trusting environments. Maybe the password is not for the computer, maybe it is for the teacher/staff WiFi. A WiFi network that has no other security aside from the password: TeacherWifi1.
Before spending thousands of budgetary funds on security consultation, all schools (and organizations) should focus on their Operational Security or OPSEC. OPSEC is officially defined as:
Operational security (OPSEC), also known as procedural security, is a risk management process that encourages managers to view operations from the perspective of an adversary in order to protect sensitive information from falling into the wrong hands.
Developing a solid OPSEC plan is not that difficult. A bit of common sense and creative thinking goes a long way. Let’s walk through some simple practices that will help improve a school’s operational security, and the school’s ability to react to problems.
Follow Normal Child Safety Practices All the Time and in all Departments
The basic child safety concepts are: keep students away from unverified adults and make sure adults are not alone with children (and if they are alone they are visible).
The standards seem to be prevalent in all child safety courses and certifications. Following these two standards, and applying them to a technology plan would yield the following rules:
- Students are never allowed on the same network as teachers/staff/guests
- Students share information through the cloud or monitored middle process (such as a Synology share that requires user login)
- Students should not be allowed to peer share with teachers (e.g. no more AirDrop)
- The guest network is limited and separated from everyone else
- No access to the network etc. unless all users provide an ID or their devices are identified as approved devices
Office and Classroom Access Should Be Managed by Policy
The worst hacking scenarios I have personally experienced, and that resulted in child and family trauma, began with data being printed and left in unattended offices/classrooms.
Simple and reasonable practice can deter most people from crossing the privacy line. Here are some suggestions:
- Laptops should be secured in a bag or other area when unattended; on the desk, lid open is bad practice
- Documenting passwords should be discouraged
- Desktops and other devices should be logged out when unattended; or secured with a password screensaver
- Teams should split their lunches and breaks to ensure that the office/classroom always has someone present
- Office/classroom hours should be posted so that everyone knows when the space is open for meetings or visitors
- Desktop phones should have a security code to make calls off-campus
- Students, parents, and others should have a demarcated area for meeting and working with staff and teachers; certain areas should remain off-limits
- Printing from offices needs to terminate in a secure space; it should be difficult for an unauthorized person to make physical contact with an office printer
Walk Around and See What You Can Do
School administrators often conduct classroom walkthroughs and observations. This process is similar.
The leadership team needs to be scheduled to break-in to areas on-campus. They should test closets, offices, doors, etc. Printers should be checked for abandoned documents, and those documents should be sampled. Did someone print and leave any confidential information? Any tests or assessments? When guests are in the building, how freely can they move beyond common areas before they are politely challenged?
The team should document what they find, and question why the access was possible. A formal review of all vulnerabilities is going to inform the necessary actions that need to be taken.
If there is a plan to work with an external contractor, having all this research is essential. Focusing on unrealistic threats and problems will not strengthen security or cybersecurity. A misaligned plan will waste resources, provide a false sense of security, and overall weaken any future response to a real threat.
Source: IT Babble Blog and Podcast
You must be logged in to post a comment.